WordPress Security Vulnerabilities Increasing
WordPress security in 2025 is a complex challenge, with vulnerabilities rampant and attackers relentless.
Key Points
- Research suggests WordPress security will face significant challenges in 2025. In 2024, there were over 7,966 new vulnerabilities, mostly in plugins.
- Maintenance and support are likely critical due to a 34% increase in vulnerabilities and over 500,000 infected websites.
Security Challenges in 2025
My WordPress hosting company, Crave, consistently moves owners and helps clean up and secure websites.
In 2024, Patchstack identified 7,966 new vulnerabilities, a 34% jump from 2023, averaging 22 daily.
- 96% plugins, often outdated
- 4% themes, often custom
- Only 7 in WordPress core, none significant.
Attackers are getting smarter, with over 500k websites infected, including:
- SEO spam at 422,466 incidents
- Malicious redirects at 175,520
Nearly half of the vulnerabilities were caused by Cross-Site Scripting (XSS), and 43% required no authentication, making exploitation easier.
Maintenance and Support is Critical
Maintenance and support are non-negotiable for revenue-generating businesses.
A third (33%) of vulnerabilities weren’t fixed in time, often from abandoned plugins, with 1,614 removed from WordPress.org, 1,450 high/medium priority. Zero-day exploits, weaponized in under 48 hours, underscore the need for constant updates and monitoring.
WordPress sites are vulnerable without maintenance, especially with AI potentially introducing new code vulnerabilities. Support ensures crucial backups, as 70% of recovered sites in 2024 had them, preventing total loss.
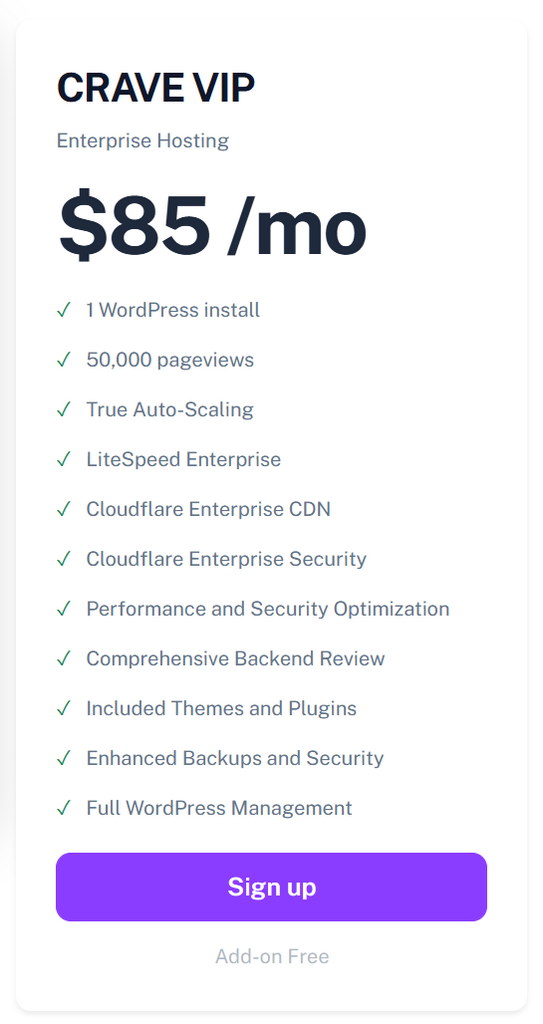
Enterprise Hosting with WordPress Management
Crave Hosting’s VIP plans with WordPress Management (WPM) offer a solution for handling updates, security monitoring, and backups. This ensures sites stay updated, reduces risk, and includes proactive measures that align with Patchstack’s findings on the importance of real-time vulnerability detection.
WordFence
I hate to burst your bubble, but this plugin creates a false sense of security. Worse yet, it’s last in the user’s journey, or in this case malware, exploit, etc.
User Journey:
- Public Internet
- Cloudlare
- Server
- WordPress
- Theme
- Plugins (WordFence)
#2 – Cloudflare
Users, including bad actors, must pass through Cloudflare before reaching your server. Critical security components include Rules, DDoS, Bots, and WAF, all working together to ensure bad actors never reach your server or WordPress.
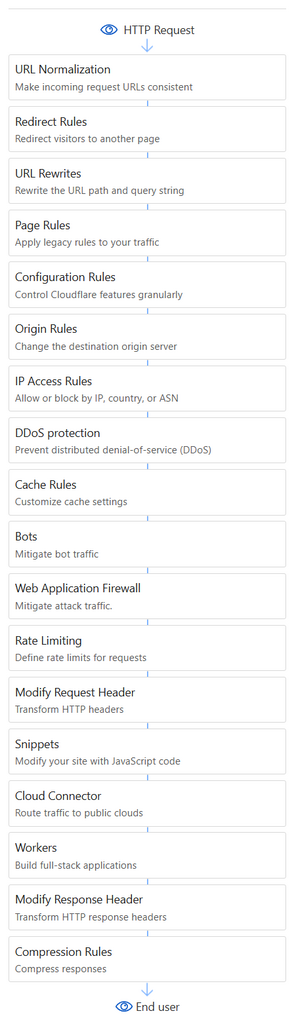
#3 – Server
Further security enhancements like IPtables, Fail2ban, and malware scanning and detection happen BEFORE users reach WordPress.
These things alone render WordFence useless. Services and plugins like this were created for scenarios that do not include enterprise solutions.
Cloudflare’s Enterprise Rules, DDoS, and WAF are infinitely better than WordFence.
Our hosting service even changes the default wp-admin login and layers additional security measures for increased security.
WordPress Overall
WordPress is, hands down, one of the easiest and least expensive ways to create an online business.
Use WordPress to operate your business and avoid using WordPress itself as a security measure—it’s NOT.
WordPress security in 2025 will be complex, with rampant vulnerabilities and relentless attackers. Maintenance and support are essential for revenue-generating businesses.
Site owners should consider the evidence. A single incident can tank core web vitals, impact rankings, and even decimate them (Japanese Keyword Hack) and naturally impact revenue.
We’ve already saved more sites than I can count and recommend looking at Crave VIP plans for your business.
Crave just started collecting video testimonials, and I’m happy to say the feedback is fantastic.